Broadening cybersecurity innovation
Field experts in the School of Computing and Augmented Intelligence showcase research at the USENIX Security Symposium

In an increasingly interconnected digital world, the exploration of groundbreaking cybersecurity research is key to fostering a safe and secure online environment.
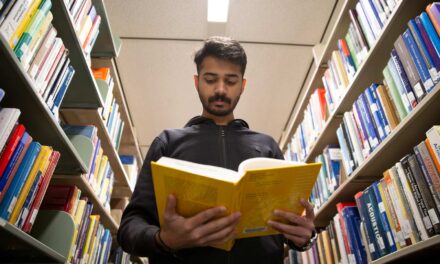
Researchers in the School of Computing and Augmented Intelligence, part of the Ira A. Fulton Schools of Engineering at Arizona State University, are among the leaders revolutionizing the security field, working to safeguard digital infrastructure and protect privacy online.
Faculty members recently attended the U.S. Defense Advanced Research Projects Agency’s AI Forward event to discuss security trends with the U.S. Department of Defense and brainstorm solutions to bridge innovations in artificial intelligence within the security field.
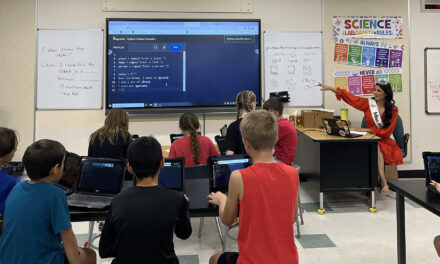
As the school’s cybersecurity experts continue working to advance efforts in digital safety, they joined their peers at the 32nd annual USENIX Security Symposium. The conference brings together researchers, practitioners, system administrators, system programmers and others interested in the latest advances in the security and privacy of computer systems and networks.
Showcasing research
Hosted by USENIX: The Advanced Computing Systems Association, the conference was held in Anaheim, California, from August 9 to 11. Faculty members and students representing the School of Computing and Augmented Intelligence presented a total of eight research papers, spanning topics including breaking wireless protocols, logs and auditing, memory, graphs and security, adversarial applications, embedded systems and firmware, robust learning and vulnerabilities and threat detection.
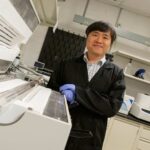
Xusheng Xiao, a Fulton Schools associate professor of computer science and engineering, showcased research on cyber threat detection and identification techniques. He notes that his work focuses on protecting enterprises, or large organizations, improving the detection of cyberattacks and investigating any damage inflicted after an attack.
“Normally, the root cause of a cyberattack is that attackers are compromising the low-hanging fruit that is easy to access, like machines that connect to the internet externally and can be compromised by downloading malware or inserting a USB,” Xiao says. “We’re looking at how to implement algorithms that make it more practical for companies to avoid the vulnerabilities that lead to equipment being compromised.”
Xiao outlines the cost-effectiveness of this practical approach that helps to make it more accessible in his research paper titled “DistDet: A Cost-Effective Distributed Cyber Threat Detection System.” He presented this research at the conference, in addition to another work titled “On the Security Risks of Knowledge Graph Reasoning” which addresses security threats in knowledge graph reasoning technology.
Adil Ahmad, an assistant professor of computer science and engineering in the Fulton Schools, also shared his research at the conference, exploring how to build a new operating system design to create and keep more robust logs for forensic analysis.
“Logs are a very important aspect of all machines and help us keep track of what’s going on. So, if something bad happens within an enterprise, we can track what went wrong,” Ahmad says. “Our research points out the pitfalls in logging system designs to improve the collection of logs and make them secure against attacks that can even compromise operating systems.”
Ahmad notes that this research is done in collaboration with Microsoft Research and has the potential to contribute to securing log collection within Microsoft Windows tools in the future.
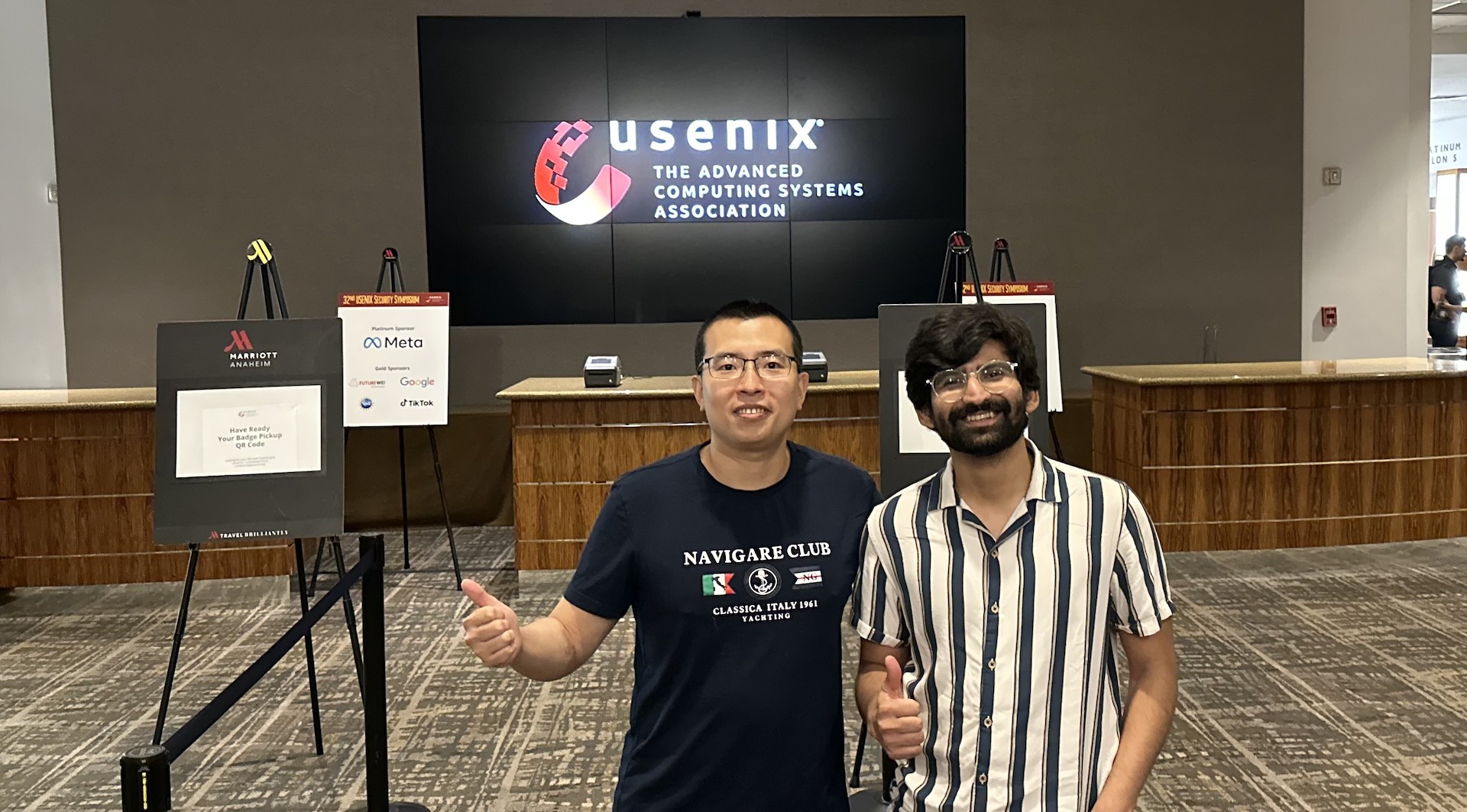
Xusheng Xiao (left) and Adil Ahmad (right) pose at the 32nd annual USENIX Security Symposium, which was held in Anaheim, California, from August 9 to 11, 2023. Photo courtesy of Xusheng Xiao
School-wide participation
Xiao and Ahmad were joined by members of ASU’s Security Engineering for Future Computing, or SEFCOM, team, a laboratory within the School of Computing and Augmented Intelligence that produces innovative research projects, assurable development and hands-on training programs in the areas of cyberspace security and defense.
SEFCOM members Adam Doupé, an associate professor of computer science, and Ruoyu “Fish” Wang, an assistant professor of computer science, attended the conference and presented research from their lab.
Research for SEFCOM’s paper titled “Greenhouse: Single-Service Rehosting of Linux-Based Firmware Binaries in User-Space Emulation” was conducted entirely by ASU faculty members and students from the lab. The work supports the need for scaling current analysis techniques to match the growth of Internet of Things devices. To do so, researchers propose a novel technique for rehosting firmware through an approach called user-space single-service rehosting, which emulates a single firmware service in user space.
Wang also showcased another paper titled “MTSan: A Feasible and Practical Memory Sanitizer for Fuzzing COTS Binaries,” which explores fuzzing and how to apply it to binary data sequences. The research demonstrates that the effectiveness and efficiency of this data-testing process is diminished by the lack of memory sanitizers for binaries, or a detector used to evaluate uninitialized memory in binary data sets in programming languages. The paper suggests the use of an alternative, more practical memory sanitizer called MTSan.
Exploring themes and future trends
“The USENIX Security Symposium is one the best conferences related to computer security in the world, especially when it comes to systems-oriented security and practical security work,” Ahmad says.
Xiao agrees, saying that “conferences like these are a very exciting opportunity to see how colleagues in similar focus areas are advancing their research.”
Looking toward future advancement, Ahmad is excited about some of the themes from the conference presentations he attended. Many of the research presentations surrounded the kernel, or the core of a computer’s operating system, that allows software to securely access hardware.
“Many researchers are exploring aspects of the kernel that lead to it getting compromised, or trying to find what the critical problems are after a kernel is compromised,” he says. “Operating system kernels are very hard to secure because they are so huge, and this area is my bread and butter so I love to see advancement.”
Ahmad also attended presentations on mixed reality and virtual reality domains, exploring how a virtual reality headset can be compromised by cyber attackers to gain information about its location by creating a 3D spatial environment.
“Identifying security and privacy risks and how to mitigate them while keeping the functionality of these mixed reality headsets is going to become a very important topic in the future, in my opinion,” Ahmed says
Xiao notes that conference participation helps establish the Fulton Schools among other cybersecurity leaders.
“Having a strong presence of our faculty members at top-tier conferences helps us demonstrate the strength of security researchers in the School of Computing and Augmented Intelligence,” he says.