Fixing the finding of faults
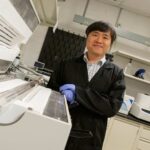
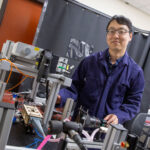
Shoshitaishvili wins DARPA Young Faculty Award for binary analysis

Imagine a factory filled with manufacturing equipment. Workers efficiently orchestrate the whir and hum of daily operations, but then an alarm sounds and the production line shuts down.
What happened? Did a faulty new device unleash the problem when it was brought into use for the first time? Or did a component suddenly fail within a machine already running at the heart of the plant?
Computer scientists ask similar questions when they seek to find and fix “bugs” or lapses in the integrity of software maintaining vital communications, infrastructure and security systems. Can the issue be identified by static analysis, perusing configurations of code? Or does the situation require dynamic analysis of programs while they are executing code and driving processes?
“Dynamic approaches dominate the field of binary analysis because of the actionability of results. If they tell you there’s a bug, there’s definitely a bug,” says Yan Shoshitaishvili, an assistant professor of computer science in the Ira A. Fulton Schools of Engineering at Arizona State University. “But they work only for the sections of software you observe running, and the burden of testing all the parts of complex applications would be untenable. In fact, the code coverage [or the portion of executed code that can be examined] for dynamic analysis is normally just 60%.”
This limitation means almost half of the space in which software bugs might be hidden, or occluded, remains unsearched by any given method of dynamic analysis. Alternatively, static analysis can reveal bugs that evade dynamic approaches; but it faces limits in terms of precision, scalability and reproducibility. So, neither method seems capable of fully revealing hidden vulnerabilities.
“That’s why my colleagues and I started exploring whether we can combine these two approaches,” Shoshitaishvili says. “One of our ideas uses a form of static analysis to identify potential bugs and also where within code they may be located. Doing so enables the extraction of specific pieces of software for subsequent dynamic testing, which is much more effective than trying to test entire applications.”
Shoshitaishvili and his team have completed preliminary work on this novel system, which they call Resin — a reference to the material used to plug holes in boat hulls. They now need to determine how their approach can be applied to yield maximum impact for keeping vital software shipshape.
The potential of this innovative work has captured the attention of the Defense Advanced Research Projects Agency, or DARPA, a U.S. Department of Defense entity that fosters the development of breakthrough technologies to enhance national and global security.
DARPA has chosen Shoshitaishvili for a 2022 Young Faculty Award, which identifies him as a rising star among university scientists, engineers and mathematicians. Awardees receive funding, mentorship and professional contacts that support their research and its application to defense and security issues. Shoshitaishvili’s award includes $500,000 distributed across two years, with the possibility of another $500,000 for a third year.
“I’m just over the moon that my work is being recognized for its potential to help DARPA advance both the state of science and societal security,” Shoshitaishvili says. “I’m particularly excited about this award because it allows me to interface with an agency that engages with researchers and the direction of their projects. So, I’m very appreciative.”
Shoshitaishvili says the basis for his current research emerged during graduate studies at the University of California, Santa Barbara, when he worked with former fellow doctoral student and current Fulton Schools faculty peer Ruoyu “Fish” Wang to create a novel technology for binary code analysis.
“It’s called angr, and it enabled our successful team performances during DARPA Cyber Grand Challenge hacking competitions,” he says. “But it has become a building block for a lot of technology research. It’s been cited in academic papers nearly 1,000 times. Resin is now intended to be another block on top of the foundation that angr created. It will offer a set of techniques to identify occluded bugs, but it will also be a functional prototype that can be used to generate real outcomes.”
Shoshitaishvili also says his achievements in cybersecurity reflect the caliber of his colleagues in the School of Computing and Augmented Intelligence, one of the seven Fulton Schools at ASU. Alongside Wang, he points to the inspiration of Adam Doupé, an associate professor of computer science and fellow UC Santa Barbara alum.
“When I was interviewing for my role here in 2017, there was already a great security team in place,” Shoshitaishvili says. “But I remember talking to Adam and learning that there was a plan in place to create the top university security team in the world. That’s a real vision, and we are making it happen. By this coming fall, we’re going to have more than a dozen faculty members in cybersecurity, which makes us one of the biggest departments in the country.”
Complementing his praise for peers, Shoshitaishvili is recognized by the school administration for his highly innovative efforts to eliminate software vulnerabilities and his broader value to the work of the Fulton Schools.
“Yan is a star researcher and an up-and-coming leader in cybersecurity,” says K. Selçuk Candan, a professor of computer science and engineering as well as a co-director of the School of Computing and Augmented Intelligence. “We are proud to see that his contributions to the field and the real-world impact of his research are now being recognized through this highly prestigious award.”
Shoshitaishvili is the 15th ASU faculty member to receive the DARPA Young Faculty Award since its inception in 2007. Other recent Fulton Schools recipients include: Saeed Zeinolabedinzadeh, an assistant professor of electrical and computer engineering, who was recognized in 2020; Yu Yao, an assistant professor of electrical engineering, who was recognized in 2019; and Sze Zheng Yong, an assistant professor of mechanical engineering, who was recognized in 2018.