Countering counterfeits and reinforcing reliability in electronics
Accidentally purchasing a counterfeit product usually results in an inferior product and mild annoyance for the average consumer, but if the military receives a counterfeit computer chip it can mean major security and reliability issues with failures at critical moments.
“U.S. defense security is very worried about cyberattacks,” says Hugh Barnaby, associate professor in electrical engineering. “They’re worried about what we think of as ‘Trojan horses,’” which, in this case, are counterfeit integrated circuit chips masquerading as the real deal.
While most highly publicized hacks are based in software, it’s also possible to hack hardware. When a company like Intel or IBM manufactures its chips in another country, there’s a significant concern of tampering or the production of substandard chips that can result in dire consequences.
“Say you have an IC chip that’s designed to enable access from an external actor,” Barnaby says, “They can access and steal intellectual property, spy, or have a system break down while performing a task. Anyone from the U.S. Air Force to Intel to a political party is susceptible.”
One way for malicious actors to compromise hardware is to exploit reliability threats, Barnaby says, so in order to ensure electronics are secure enough to withstand hardware attacks is to make them more reliable. Barnaby is working on multiple projects to make electronics more resilient in this regard.
Ensuring electronic reliability with DARPA
The Defense Advanced Research Projects Agency is funding a project focused on developing techniques for modeling reliability in high-end integrated circuit electronics. Reliability involves making something last longer until it starts to break down or, at the very least, understanding when it’ll break down to limit unpredictable failures.
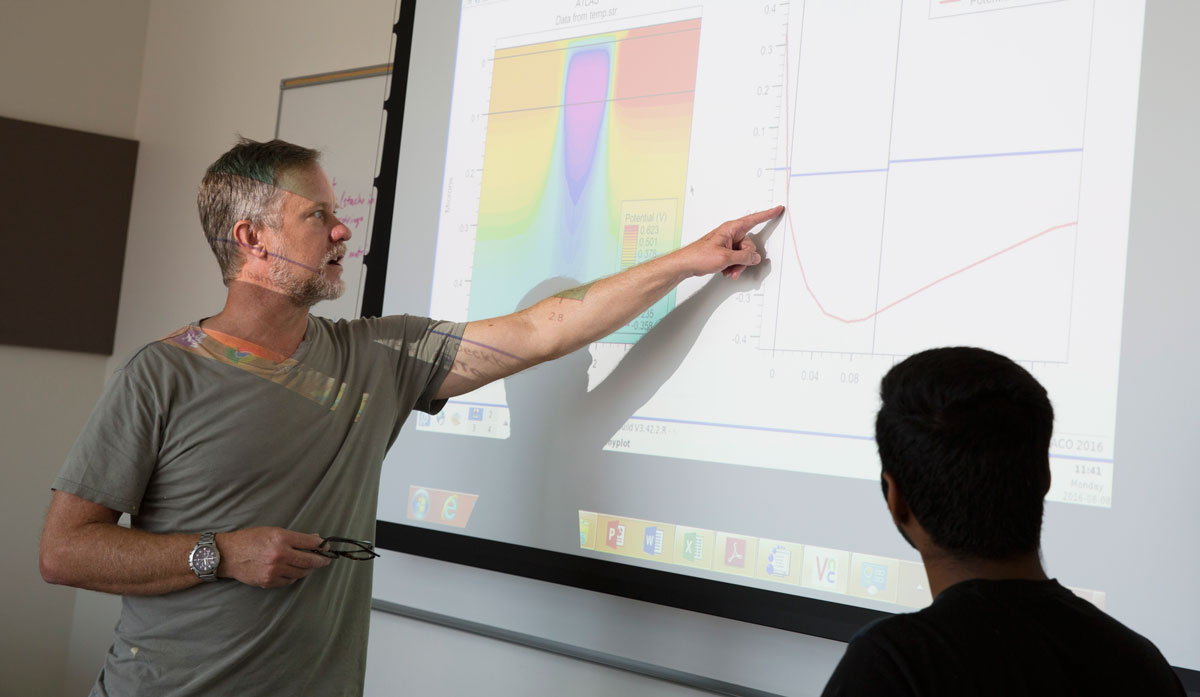
Barnaby and his hostile environment electronics research team of four graduate students are part of a one-year, $700,000 DARPA-funded Integrity and Reliability of Integrated Circuits program in partnership with the University of Southern California to develop models that help designers account for reliability effects.
Counterfeit chips are often not nearly as reliable as the ones that come from original manufacturers. Inserting less reliable components into electrical systems — whether it be an unintentional outcome of manufacturing or done intentionally as a malicious attack — can pose severe threats to hardware infrastructure.
Traditionally, understanding electronics reliability has come from “post mortem” analysis where an “autopsy” is performed on a device, which destroys the actual hardware, is time consuming and expensive. DARPA is looking to test reliability in a less destructive way.
“They want us to develop modeling techniques that enable us to do this autopsy virtually, without destroying it,” Barnaby says. “Cost and speed are better when doing it in software.”
DARPA wants researchers to use the current understanding of IC aging mechanisms to develop new diagnostic testing techniques. Such diagnostics may help industrial and defense systems analysts more quickly identify and respond to the reliability threat posed by counterfeit systems.
Barnaby’s approach is to go right to the source.
“The way you make an IC is you use computers to help design it,” Barnaby says. “It helps to have features that are put in at the design phase that help you model the reliability.”
A transition from radiation to reliability
Modeling reliability issues is a logical next step beyond Barnaby’s traditional focus on issues related to radiation, which can also cause electronics to operate poorly or fail. In this area, Barnaby’s research has contributed to a recent $100,000 NASA program to understand and model radiation effects for satellites and other space vehicle electronics.
“The effects are similar between radiation and breaking down [due to reliability issues],” Barnaby says. “The fundamental mechanisms are very similar so I can use my understanding of the effects of radiation to model the effects of what we call operational stress.”
A patented approach to modeling electronic failures
Barnaby’s recent work builds on experience in developing a patent through Arizona Technology Enterprises that models the impact or damage to the materials of an integrated circuit as a result of operational stress. The designer using this modeling technique can see operational stress effects in real time.
The patented method models the very tiny deep submicron transistors in complementary metal oxide semiconductors — CMOS circuits, the standard technology platform used in most integrated electronics today.
Defects build up in the circuit material at the deep submicron level as the circuit ages by a number of mechanisms, particularly the negative bias temperature instability and hot carrier injection causes of defects. As these defects build up they change the operation of the IC, causing reliability issues and, ultimately, failures.
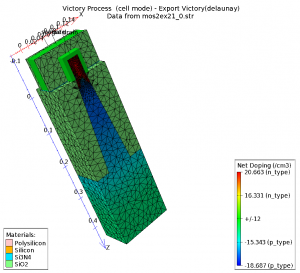
Using Silvaco’s TCAD device simulation tool, Barnaby’s team can study advanced electronic devices, such as this FINFET, and model different mechanisms of reliability. Graphic courtesy of Silvaco
Barnaby’s success with his modeling patent was helped by ASU’s relationship with software company Silvaco, which provides its software tools to universities through its Silvaco University Program.
“This industry collaboration gives us access to tools that let us do pretty advanced work for DARPA in reliability,” Barnaby says.
The company’s tools, such as its TCAD device simulation tool, are built with modeling in mind, in addition to product design.
“It enables me to model device physics as well as integrated circuits in a very flexible way,” Barnaby says.
New collaboration set to create new physical security features
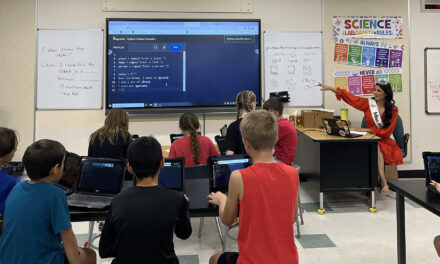
Barnaby is also working on electronic security beyond modeling with electrical engineering Professor Michael Kozicki, whom he’s previously worked with on radiation effects on space and medical electronics. Through the Exploiting Nanomaterials for End-to-End Cybersecurity Solutions project — a collaboration between ASU, Northern Arizona University and the University of Arizona that is funded through the Arizona Board of Regents Innovation Fund — they’re finding new ways to authenticate hardware for cybersecurity purposes.
They’re exploring a connection between Kozicki’s research in conductive bridging RAM memory technology and Programmable Metallization Cell technology, in which he holds several dozen key patents, to create “fingerprints” on electronics that will make them more secure.
“The flexibility of the technology allows us not only to address issues with space electronics, but also cybersecurity,” Barnaby says. “It’s a nice niche that complements our existing efforts with DARPA and NASA.”
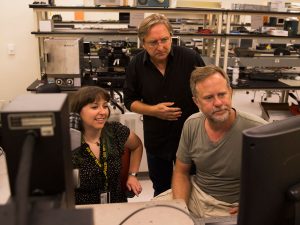
Kozicki (center) and Barnaby are researching new physical cybersecurity methods as part of a tri-university research project. Photographer: Jessica Hochreiter/ASU
Through Kozicki’s memory technology, they found two ways to derive uniquely identifying “fingerprints” on a chip, one via the electronic elements and another via the physical components.
The first exploits the inherent variability of the current flowing through switching devices. In the design process this variation at the nanoscale level is normally ignored, but Kozicki looks to the random nature of current variation to generate unique random codes to encrypt information.
The second uses dendrites, the metallic growths in a dielectric — a key material in CMOS — as a result of metal ion migration from the interconnections within the IC. Each dendrite is a unique and complex fractal pattern, which looks like a two-dimensional tree, and can be used as an identification mark for a specific chip.
“We specialize in using things that are normally avoided by the industry and use them to good effect,” says Kozicki, the principal investigator on the project.
They aim to leverage their expertise in electronic materials and devices combined with NAU’s cybersecurity strengths and UA’s optical processing strengths to develop new cybersecurity methods to prevent theft and corruption of information and keep counterfeit parts out of critical applications such as aircraft, cars and medical devices.
Media Contact
Monique Clement, [email protected]
480-727-1958
Ira A. Fulton Schools of Engineering